Deconstructing Technology: The Broad Spectrum of Human Innovation
At its most fundamental, technology is an incredibly broad concept. It encompasses the application of scientific knowledge for practical purposes, especially in industry. It represents the tools, machines, techniques, crafts, systems, and methods of organization that are invented or discovered to solve problems, extend human capabilities, or achieve specific goals. From the earliest flint tools crafted by our ancestors to the most advanced AI algorithms shaping our future, technology is about creation, invention, and the practical application of knowledge.
Reviewed by technology strategists and digital marketing practitioners with backgrounds in enterprise IT, SaaS, and startup growth. Contributors hold credentials including ITIL v4 certification, AWS Solutions Architect, Google Analytics certification, and hands-on experience at Series A-C startups and Fortune 500 tech divisions. Content is cross-referenced against industry reports from Gartner, McKinsey, IDC, and the World Economic Forum. Last reviewed: March 2026.
Consider the expansive history of human progress. The invention of the wheel, the printing press, the steam engine, electricity, vaccination, and the automobile are all monumental technological advancements. Each represented a novel way of doing things, a new tool, or a new process that fundamentally altered societies and economies. These innovations weren’t necessarily about managing information; they were about transforming physical labor, enabling mass production, facilitating travel, or improving health outcomes. They expanded what was possible.
-
Innovation Across Industries
Technology manifests in virtually every sector imaginable. In agriculture, we see precision farming technologies, GMOs, and advanced irrigation systems. In medicine, there are robotic surgeries, gene editing tools, and sophisticated diagnostic equipment. Manufacturing relies on automation, 3D printing, and advanced materials science. Even in fields like art and design, new technologies continually push creative boundaries, from digital painting software to virtual reality experiences.
-
The Purpose of Technology
The core purpose of technology is to solve problems, enhance efficiency, and create new possibilities. It’s about how things are made, how tasks are performed, and how human potential is amplified. A new type of battery, a more efficient solar panel, a breakthrough in quantum computing – these are all examples of technology. They represent the cutting edge of human ingenuity, pushing the boundaries of what we can achieve.
-
Technology as a Catalyst for Change
For tech entrepreneurs, understanding technology in this broad sense means recognizing the fundamental innovations that drive markets. It’s about identifying unmet needs and creating novel solutions, whether that’s a new material, a new energy source, or a new way to interact with the world. This perspective encourages a mindset of invention and disruption, focusing on the core mechanisms and principles behind new capabilities.
Understanding Information Technology: The Digital Backbone of Modern Business
While technology is the broad universe of tools and processes, information technology (IT) is a specialized, yet incredibly pervasive, subset. IT specifically refers to the use of computers, storage, networking, and other physical devices, infrastructure, and processes to create, process, store, secure, and exchange all forms of electronic data. It is the infrastructure and systems that enable the management and flow of information within an organization and across the globe.
Think of IT as the nervous system of a modern business. It comprises the hardware (servers, workstations, mobile devices), software (operating systems, applications, databases), networks (LANs, WANs, the internet), and the people and processes that manage them. The primary goal of IT is to ensure that information is accessible, secure, and useful for decision-making and operational efficiency. Without robust IT, businesses would struggle to communicate, process transactions, store customer data, or even manage their payroll.
-
The Components of IT
An organization’s IT landscape is complex and multifaceted. It includes:
- Hardware: Servers, computers, mobile devices, routers, switches, data centers.
- Software: Operating systems, enterprise resource planning (ERP) systems, customer relationship management (CRM) software, productivity suites, specialized applications.
- Networks: The infrastructure that connects all devices and allows for data exchange, both internally and externally.
- Databases: Systems for storing, organizing, and retrieving vast amounts of structured and unstructured data.
- Cloud Services: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), Software as a Service (SaaS) that provide scalable computing resources over the internet.
- IT Services: Help desk support, system administration, network management, data backup and recovery, and cybersecurity operations.
This comprehensive collection of interconnected elements forms what is commonly referred to as a Tech Stack. For a startup, defining and optimizing its tech stack is crucial. It involves choosing the right combination of programming languages, frameworks, databases, servers, and front-end tools that will power your product and operations. A well-designed tech stack ensures scalability, performance, and maintainability, directly impacting your ability to deliver value and innovate rapidly.
-
Evolution and Modern Relevance
From the mainframe computers of the mid-20th century to the ubiquitous cloud-based systems and mobile computing of today, IT has undergone a profound evolution. Today, IT is not just a support function; it’s a strategic enabler. It powers e-commerce, facilitates global communication, supports remote workforces, and underpins the collection and analysis of massive datasets. For many businesses, particularly tech startups, their IT infrastructure is their competitive advantage.
-
Focus on Information Management
The core focus of IT is on managing information lifecycle – from its creation and capture to its storage, retrieval, processing, and eventual archival or destruction. This involves ensuring data integrity, availability, and confidentiality. It’s about making sure the right information gets to the right people at the right time, in a secure and efficient manner.
The Core Distinctions: Scope, Focus, and Application
-
Scope: Broad vs. Specific
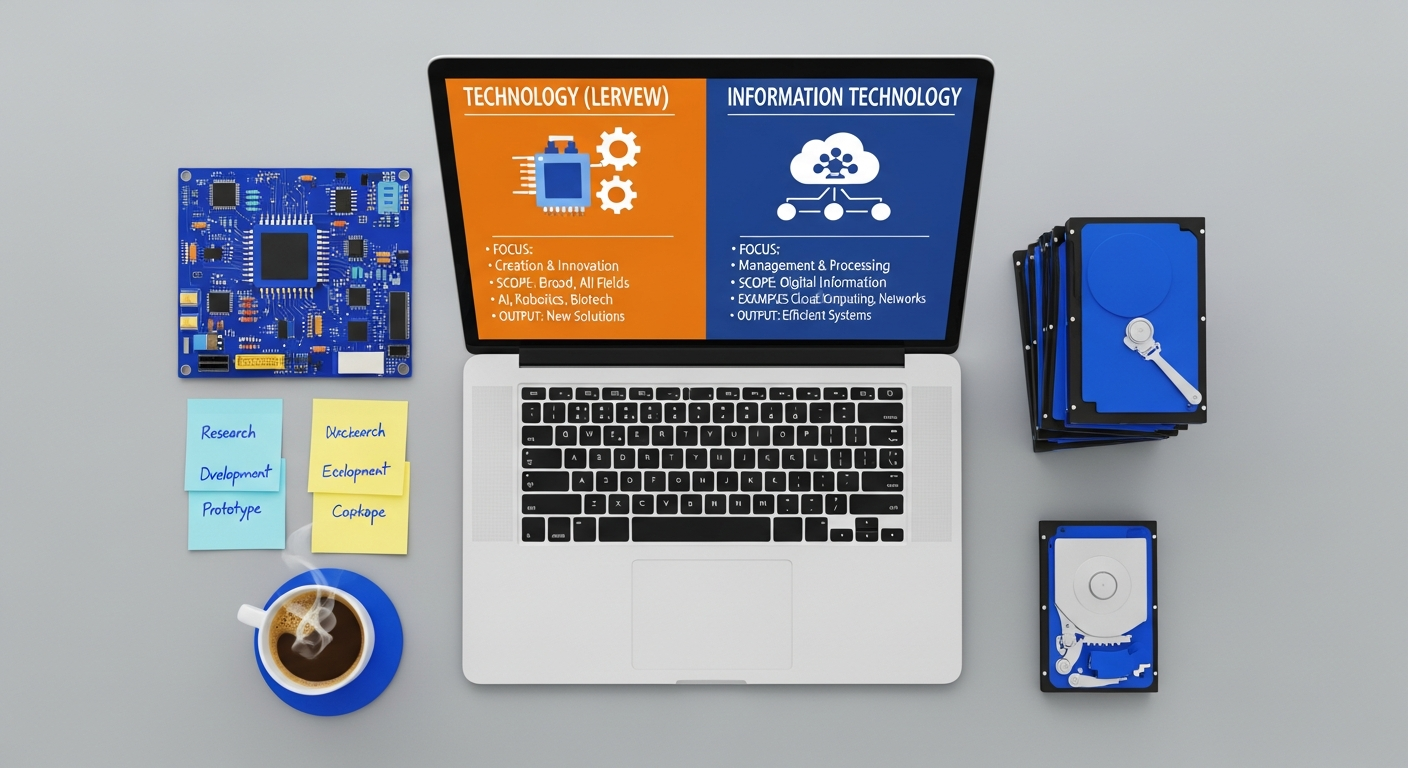
The most significant difference lies in scope. Technology is an overarching term that covers any method, tool, or knowledge applied to solve a problem or achieve a goal. This includes mechanical technology, biotechnologies, material sciences, and, of course, digital technologies. It’s the entire universe of applied knowledge.
Information Technology (IT) is a specialized segment within this vast universe. It specifically deals with the use of digital tools and systems for managing information. All IT is technology, but not all technology is IT. For example, a new type of hybrid engine is technology, but it’s not IT. The software that manages the engine’s performance, however, would be IT.
-
Focus: Creation/Innovation vs. Management/Deployment
The focus of each term also diverges:
- Technology’s Focus: Primarily on the creation, invention, and advancement of new tools, techniques, or processes. It asks, “What new things can we build or new ways can we do things?” Its goal is often to innovate and expand human capabilities.
- Information Technology’s Focus: Primarily on the deployment, management, and optimization of existing digital tools and systems to process and exchange information efficiently and securely. It asks, “How can we best use digital tools to manage our information and operations?” Its goal is operational excellence, data integrity, and business enablement.
Consider a self-driving car. The advanced sensors, AI algorithms for perception and decision-making, and robotic controls are all examples of core technology. The robust network infrastructure within the car, the cloud-based data storage for map updates, and the communication protocols that allow the car to send and receive data are all aspects of information technology enabling that core technology to function and improve.
-
Application: Product/Solution vs. Infrastructure/Operations
The application of each concept also provides a clear differentiator:
- Technology’s Application: Often seen in the core product or service itself. A startup building a new AI-powered diagnostic tool is developing a core technology. A company developing a new renewable energy source is innovating in technology.
- Information Technology’s Application: Primarily in the internal and external infrastructure that supports business operations. The systems that manage customer data, facilitate internal communication, host the company’s website, or secure intellectual property are all applications of information technology.
A software development firm creates new software (technology). The internal systems they use to manage their code repositories, track bugs, communicate between teams, and deploy their products are all part of their IT infrastructure.
Strategic Implications for Tech Entrepreneurs and Business Leaders

Understanding the “technology vs information technology key differences” isn’t an academic exercise; it has profound strategic implications for how you build, manage, and grow your tech startup in 2026. Misinterpreting these terms can lead to misallocated resources, inefficient operations, and missed opportunities.
-
Investment and Resource Allocation
For a startup, differentiating between technology development and IT infrastructure is crucial for budget allocation. Are you primarily investing in building a groundbreaking new technology (R&D, product development, engineering talent), or are you investing in robust IT systems to support your internal operations, scale your existing services, or secure your data (servers, network upgrades, cloud services, IT support staff)? Both are vital, but their strategic funding streams and expected returns differ.
A deep tech startup might allocate 80% of its budget to core technology R&D, with 20% for essential IT. A SaaS company, while developing new software features (technology), might also dedicate significant resources to its IT operations to ensure uptime, data security, and seamless customer experience.
-
Talent Acquisition and Organizational Structure
The distinction directly impacts your hiring strategy. You need different skill sets for technology innovation versus IT management. A “technologist” (e.g., a research engineer, a data scientist, a product developer) focuses on creating new technological solutions. An “IT professional” (e.g., a network administrator, a cybersecurity analyst, a system architect) focuses on maintaining, securing, and optimizing the existing information systems.
Your organizational chart should reflect this. A Chief Technology Officer (CTO) typically leads technology innovation and product development, looking outward at market trends and future possibilities. A Chief Information Officer (CIO) or Head of IT focuses on internal IT operations, ensuring reliability, security, and efficiency. Confusing these roles can lead to strategic drift and operational bottlenecks.
-
Risk Management and Cybersecurity Best Practices
This is where the IT side becomes critically important for business continuity and reputation. While a new technology might carry market adoption risk, your IT infrastructure carries operational and security risks. Implementing robust Cybersecurity Best Practices is not just an add-on; it’s fundamental to your IT strategy. This includes:
- Data Encryption: Protecting sensitive data at rest and in transit.
- Access Control: Implementing strong authentication and authorization mechanisms (e.g., MFA, least privilege).
- Regular Backups: Ensuring business continuity in case of data loss or system failure.
- Incident Response Plan: A clear strategy for detecting, responding to, and recovering from security breaches.
- Employee Training: Educating staff on phishing, social engineering, and secure computing practices.
- Vulnerability Management: Regularly scanning systems for weaknesses and applying patches.
A breach in your core technology might expose a flaw in your product, but a breach in your IT infrastructure can compromise all your sensitive data, disrupt operations, and severely damage customer trust and regulatory compliance. Investing in strong IT security is an investment in your company’s foundation.
-
Market Positioning and Communication
Clearly defining whether your startup offers a new technology or an IT service (or both) is vital for your brand messaging, investor pitches, and customer communication. Are you selling a groundbreaking AI algorithm (technology) or a managed IT service that leverages existing cloud technologies (information technology)? Precision here ensures you attract the right talent, investors, and customers.
The Interplay and Synergy: Where Technology and IT Converge
While distinct, technology and information technology are not isolated silos. In the modern digital economy, they are deeply interdependent, creating a powerful synergy that drives innovation and business growth. The most successful enterprises in 2026 will be those that effectively leverage this interplay.
-
IT as an Enabler of New Technologies
Many cutting-edge technologies would not be possible without a robust IT foundation. Consider Artificial Intelligence (AI) and Machine Learning (ML). While the algorithms themselves are core technology, their development and deployment require massive computing power, vast data storage, and high-speed networking—all hallmarks of sophisticated IT infrastructure. Cloud computing, a core IT offering, provides the scalable resources necessary for training complex AI models without prohibitive upfront costs.
Similarly, the Internet of Things (IoT) involves myriad devices (technology) generating vast amounts of data. It is the underlying IT infrastructure—the networks, data centers, and data processing systems—that collects, transmits, stores, and analyzes this information, transforming raw data into actionable insights.
-
New Technologies Reshaping IT
Conversely, advancements in core technologies constantly reshape and improve IT practices. For instance, AI and ML are increasingly being integrated into IT operations for predictive maintenance, automated security threat detection, and intelligent resource allocation. Blockchain technology, while a new form of distributed ledger technology, is finding applications in IT for enhanced data security, supply chain transparency, and digital identity management.
Serverless computing and containerization (like Docker and Kubernetes) are technological innovations that drastically change how IT teams deploy and manage applications, leading to more agile and efficient operations.
-
Digital Transformation and Business Agility
The concept of digital transformation epitomizes the convergence of technology and IT. It’s not just about adopting new digital tools (technology); it’s about fundamentally changing how a business operates, delivers value, and interacts with customers using those tools, enabled by a modernized IT infrastructure. This involves leveraging new technologies to create innovative products and services, simultaneously optimizing internal processes and customer experiences through advanced IT systems.
For tech entrepreneurs, this means your ability to innovate with new technologies is directly proportional to the strength and flexibility of your IT infrastructure. A rigid, outdated IT system can stifle innovation, while a modern, agile IT environment can accelerate it.
-
Data Analytics for Business: The Ultimate Synergy
One of the clearest examples of the synergy between technology and IT is in the realm of Data Analytics for Business. Modern IT systems are designed to collect, store, and process massive volumes of data from various sources – customer interactions, operational logs, market trends, IoT devices, and more. This data, in its raw form, is a byproduct of IT operations.
However, to extract meaningful insights and drive strategic decisions, raw data requires advanced analytical technologies. This includes:
- Business Intelligence (BI) Tools: Technologies that visualize data to identify trends and patterns.
- Machine Learning Algorithms: Technologies that predict future outcomes or classify data.
- Big Data Platforms: Technologies (like Hadoop or Spark) designed to process and analyze extremely large datasets that traditional IT systems might struggle with.
The IT infrastructure provides the data and the platform; the analytical technologies provide the intelligence. Together, they enable businesses to understand customer behavior, optimize operations, identify new market opportunities, and make data-driven decisions that are critical for success in 2026. Without robust IT, there’s no data to analyze; without cutting-edge analytical technology, the data remains untapped potential.
Future Outlook: Navigating the Evolving Landscape in 2026
As we look towards 2026 and beyond, the lines between technology and information technology will continue to blur and redefine themselves. Emerging fields like quantum computing, advanced robotics, Web3, and synthetic biology represent profound technological shifts. Each of these will, in turn, demand new paradigms for information management, security, and infrastructure, thus evolving the landscape of IT.
For tech entrepreneurs, this evolving landscape presents both challenges and unparalleled opportunities. The key will be to foster a holistic understanding: to be agile in adopting new technologies for product innovation while simultaneously ensuring that the underlying IT infrastructure is secure, scalable, and resilient enough to support these advancements. This requires:
- Continuous Learning: Staying abreast of both technological breakthroughs and best practices in IT management.
- Strategic Foresight: Anticipating how new technologies will impact your IT needs and vice-versa.
- Integrated Planning: Developing strategies that consider product technology development and IT infrastructure as two sides of the same coin, rather than separate entities.
In essence, successfully navigating the future means recognizing that while technology inspires what’s possible, information technology makes it practical, manageable, and secure. Both are indispensable pillars of the modern enterprise.
Understanding the “technology vs information technology key differences” is not just about academic accuracy; it’s about strategic clarity. For tech entrepreneurs in 2026, distinguishing between these concepts empowers better decision-making in innovation, operations, resource allocation, and risk management. Technology provides the tools and solutions that push the boundaries of human capability, while information technology provides the essential infrastructure to manage, secure, and leverage information effectively. By embracing this nuanced understanding, you can build a more robust, innovative, and competitive enterprise ready to thrive in the digital age.
Frequently Asked Questions
Is software considered technology or information technology?▾
Can a company operate with technology but without formal information technology infrastructure?▾
What is the difference between a CTO (Chief Technology Officer) and a CIO (Chief Information Officer) in light of these distinctions?▾
How does cloud computing relate to the concepts of technology and information technology?▾
Why is understanding the differences between technology and information technology crucial for startups?▾
Key Frameworks, Standards, and Vendors: The IT Landscape
IT Governance and Management Frameworks
Technology leaders need a working knowledge of the frameworks that define professional IT practice:
- ITIL (Information Technology Infrastructure Library): The world’s most widely adopted IT service management framework — now ITIL 4 (released 2019, managed by Axelos). ITIL provides a set of detailed practices for IT activities such as service desk management, change management, incident management, and continuous improvement. IT job postings frequently list ITIL certification as preferred or required. Over 2 million ITIL certifications have been issued globally.
- COBIT (Control Objectives for Information Technologies): Developed by ISACA — the global IT governance and audit professional body — COBIT 2019 provides a governance framework for aligning IT strategy with business objectives. Particularly used in audit, compliance, and regulated industries (banking, healthcare, government). COBIT maps directly to ISO/IEC 38500 (corporate governance of IT) and SOX compliance requirements.
- ISO/IEC 27001: The internationally recognized standard for Information Security Management Systems (ISMS) — published by ISO and IEC, now at ISO 27001:2022. Specifies requirements for establishing, implementing, and continually improving an ISMS. Certification is increasingly required for enterprise B2B contracts and government procurement. Over 70,000 organizations are certified worldwide (ISO Survey 2022).
- NIST Cybersecurity Framework (CSF 2.0, 2024): Published by the U.S. National Institute of Standards and Technology — widely adopted voluntary framework for managing cybersecurity risk, organized around five functions: Identify, Protect, Detect, Respond, Recover. Free to use; referenced by CISA, OMB, and many state regulations. CSF 2.0 added a sixth function: Govern.
Major Cloud Providers: The Infrastructure of Modern IT
Cloud computing has transformed IT infrastructure. The three dominant hyperscalers account for approximately 65% of global cloud revenue (Synergy Research Group, Q3 2024):
- Amazon Web Services (AWS): Market leader at ~31% of global cloud infrastructure revenue. 200+ services including EC2 (compute), S3 (storage), RDS (managed databases), Lambda (serverless), and SageMaker (managed ML). AWS Certification is one of the most valued IT credentials globally. Customers include Netflix, NASA, Capital One, and the CIA.
- Microsoft Azure: ~24% market share. Uniquely positioned for enterprise Windows/Office 365 environments; deep Active Directory integration. Azure OpenAI Service (partnership with OpenAI) gives Azure a specific AI advantage. 95% of Fortune 500 companies use Azure.
- Google Cloud Platform (GCP): ~11% market share. Strongest in data analytics (BigQuery), AI/ML (Vertex AI, TPUs), and Kubernetes (GKE — Google invented Kubernetes, now open-source). Preferred for organizations with deep data science workloads.
Enterprise Software Suites: The Core of IT Operations
- SAP S/4HANA: The leading enterprise ERP (Enterprise Resource Planning) — used by 87% of global commerce across SAP’s customer base. Covers finance, HR, supply chain, procurement, and manufacturing. SAP HANA is an in-memory database optimized for real-time analytics.
- Oracle Cloud ERP: Competitor to SAP in ERP and database — Oracle Database (12c, 19c, 23ai) is the dominant RDBMS in enterprise data centers. Oracle Fusion Cloud Applications cover HCM, SCM, and ERP.
- Salesforce CRM: The category-defining cloud CRM at ~23% global CRM market share — supports sales force automation, marketing cloud, service cloud, and the Einstein AI platform. SFDC AppExchange has 7,000+ integrated apps.
- Microsoft 365 + Azure AD: The standard productivity and identity stack for enterprise organizations — Teams, SharePoint, Exchange Online, Entra ID (formerly Azure Active Directory) for identity and access management.
Key Roles: Technology vs IT Career Paths
| Technology Roles | IT Roles |
|---|---|
| CTO (Chief Technology Officer) | CIO (Chief Information Officer) |
| Software Engineer / Architect | Systems Administrator / SysOps |
| AI/ML Engineer | DevOps / SRE (Site Reliability Engineer) |
| Product Manager | Data Engineer / DBA (Database Admin) |
| R&D / Innovation Lead | CISO (Chief Information Security Officer) |
Data Privacy and Regulatory Compliance (IT’s Domain)
Regulatory compliance is one of the clearest delineators between general technology and IT:
- GDPR (General Data Protection Regulation): EU regulation effective May 2018 — the global gold standard for data privacy. Fines up to 4% of annual global turnover or €20 million (whichever is higher). GDPR compliance is fundamentally an IT responsibility: data mapping, consent management, breach notification (72-hour requirement), data subject request handling, and DSAR workflows all require IT systems and governance.
- CCPA / CPRA (California Consumer Privacy Act / California Privacy Rights Act): U.S. state-level privacy law effective 2020 (CPRA amendments 2023) — gives California consumers the right to know, delete, and opt out of sale of personal data. Applies to businesses with over $25M revenue OR processing 100,000+ consumer records annually.
- SOX (Sarbanes-Oxley Act, 2002): U.S. federal law requiring public companies to maintain internal controls over financial reporting — Section 404 mandates IT general controls (ITGCs) audit: access controls, change management, data backup/recovery, security monitoring. External auditors test IT systems directly.
Related Guides
IT Operations Tooling: The Modern Stack
ITSM Platforms: Where ITIL Meets Software
ITIL is a framework — ServiceNow is the dominant software platform that operationalizes it:
- ServiceNow: The leading enterprise ITSM platform — $10.9B revenue (FY2024), used by 85% of the Fortune 500. ServiceNow IT Service Management covers incident, problem, change, and release management on a single cloud platform. ITIL-aligned workflows are built in. The Now Platform extends to IT Operations Management (ITOM), IT Asset Management (ITAM), and HR/legal workflows. Market cap: ~$175B (2025). Competitors include Jira Service Management (Atlassian), Freshservice (Freshworks), and BMC Helix.
- IT Operations Management (ITOM): The practice of monitoring and managing IT infrastructure performance — event management, discovery, and AIOps (AI for IT Operations). ITOM tools include Dynatrace, Datadog, New Relic (APM/monitoring), PagerDuty (incident response), and Splunk (log analytics, acquired by Cisco 2024 for $28B).
- SLA / SLO / SLI concepts (DevOps/SRE standard):
- SLA (Service Level Agreement): The contract commitment — usually with external customers. E.g., “99.9% uptime guarantee” (= 8.7 hours downtime/year). Breaches typically trigger financial penalties or credits.
- SLO (Service Level Objective): The internal target — typically tighter than the SLA to create buffer. If SLA = 99.9%, SLO = 99.95% internally.
- SLI (Service Level Indicator): The actual measurement — availability percentage, error rate, latency p99. SRE teams set SLIs → SLOs → SLAs in that order.
- Error Budget: Google’s SRE book (Beyer et al., 2016) introduced error budgets — if a service has 0.1% downtime budget/month, the engineering team can ship risky changes only while budget remains. Error budgets align reliability with release velocity.
DevOps Toolchain: Infrastructure as Code
The DevOps movement (Patrick Debois coined “DevOps” in 2009, Velocity Conference) blurs the IT/software development boundary — key tooling:
- Kubernetes (K8s): Open-source container orchestration — originally developed by Google (2014), now maintained by CNCF (Cloud Native Computing Foundation). Kubernetes has become the de facto standard for deploying containerized applications at scale. 96% of organizations are using or evaluating Kubernetes (CNCF Annual Survey 2023). The abstraction it provides sits at the IT/development boundary — “Is Kubernetes an IT responsibility or an engineering one?” is a common startup org-design question; answer: typically platform engineering or DevOps/SRE teams.
- Terraform (HashiCorp): Infrastructure as Code (IaC) — enables IT teams to define, provision, and manage cloud infrastructure (EC2 instances, VPCs, load balancers, databases) in declarative configuration files rather than manual console clicks. Acquired by IBM in 2024; Terraform remains the leading IaC tool with 35M+ downloads. OpenTofu is the open-source fork.
- GitHub Actions / GitLab CI/CD: Automated CI/CD pipelines — build, test, and deploy code changes automatically. Integrating IT operations (environment provisioning, security scanning) into CI/CD pipelines is a key DevSecOps practice.
Cloud Financial Model: CapEx vs OpEx
One of the most practically important technology vs IT distinctions for startup CFOs and boards:
- Traditional IT (on-premises): Capital expenditure (CapEx) model — purchase servers, storage, networking equipment. Assets depreciated over 3-5 years on the balance sheet. High upfront cost, predictable long-term cost, requires IT staff to maintain.
- Cloud IT (AWS/Azure/GCP): Operating expenditure (OpEx) model — pay-as-you-go subscription spending. Flows through the P&L immediately. Zero upfront, highly variable (scales with usage), no maintenance burden. Preferred by VCs (improves operating leverage metrics). Downside: cloud cost overruns are common in growth-stage startups — FinOps (Cloud Financial Management) discipline is emerging to manage this.
- Cloud cost optimization tools: AWS Cost Explorer, CloudHealth (VMware), Infracost (open-source IaC cost estimation), and Cloudability help teams optimize cloud spend. The FinOps Foundation (finops.org) publishes best practices.
- Edge computing: Processing data closer to where it’s generated (IoT sensors, autonomous vehicles, retail POS) rather than centralizing in a cloud data center. Reduces latency for time-sensitive applications. Key vendors: AWS Outposts, Azure Stack Edge, Cloudflare Workers, Fastly. Gartner predicts 75% of enterprise data will be processed at the edge by 2025 (vs 10% in 2018).
Major IT Vendors and System Integrators
- Cisco Systems: Dominant in enterprise networking (Catalyst switches, ASA/Firepower firewalls, Meraki cloud networking, WebEx). Annual revenue ~$57B. The Cisco Certified Network Associate (CCNA) and Professional (CCNP) certifications are IT networking standards. Acquired Splunk for $28B (2024) to strengthen ITOM/observability.
- IBM / Red Hat: IBM acquired Red Hat (2019, $34B) — Red Hat OpenShift is the leading enterprise Kubernetes platform, Red Hat Enterprise Linux (RHEL) is the dominant enterprise Linux distribution. IBM Consulting (80,000+ practitioners) is a major system integrator for SAP, Salesforce, and hybrid cloud deployments.
- VMware (Broadcom): Acquired by Broadcom in 2023 for $69B — VMware vSphere is the dominant enterprise virtualization platform; most enterprise data centers run on ESXi hypervisors. Broadcom’s acquisition created significant customer transition to cloud-native alternatives.
- Accenture: World’s largest technology consulting and services company (~$64B revenue, 750,000+ employees). Major system integrator for SAP, Oracle, Salesforce, and cloud migration projects. Accenture Technology aligns closely with the IT vs broader technology distinction — IT delivery is their core business.
Startup Decision Matrix: IT vs Technology Investment
| Stage | IT Priority | Technology (R&D) Priority |
|---|---|---|
| Pre-Seed / Seed | Cloud hosting (AWS/GCP), basic security (MFA, password manager), G Suite / Microsoft 365, GitHub | Product MVP, core engineering team, foundational IP |
| Series A | MDM (mobile device management), SSO (Okta/Duo), CRM (Salesforce/HubSpot), SOC 2 Type II preparation, ITIL-aligned helpdesk | Product-market fit refinement, platform engineering, data infrastructure |
| Series B+ | Dedicated IT/InfoSec team, ISO 27001 / SOC 2 Type II certification, ERP evaluation, disaster recovery planning, GDPR/CCPA compliance program | R&D team expansion, ML/AI capabilities, patent portfolio, technical moat |
| Pre-IPO / Enterprise | CISO hire, SOX IT controls, enterprise ITSM (ServiceNow), global infrastructure, M&A IT integration playbooks | CTO/VP Eng leadership, open-source contributions, industry standards participation (IEEE, CNCF) |
Key Concepts That Bridge Technology and IT: ICT, OT, and the Expanding Ecosystem
ICT: Information and Communications Technology
ICT (Information and Communications Technology) is the umbrella term used by the United Nations, OECD, and most government bodies to describe the combined field of IT plus telecommunications. ICT explicitly includes fixed-line telephony, mobile networks, internet infrastructure, satellite communications, and broadcast technology alongside traditional IT systems. The distinction matters in policy contexts: when the ITU (International Telecommunication Union) reports on global connectivity, it uses “ICT access” to measure phone, internet, and computing access together. When you encounter ICT in job titles, government programs (e.g., India’s “Digital India” initiative, the EU’s ICT Standardization work), or academic research, it signals a broader scope than IT alone — encompassing the infrastructure by which information is communicated, not just managed.
Operational Technology (OT): When IT Meets the Physical World
Operational Technology (OT) is a category of technology that is neither traditional IT nor consumer technology — it encompasses hardware and software that monitors or controls physical equipment, processes, and events in industrial environments. Examples include:
- SCADA systems (Supervisory Control and Data Acquisition) — monitor and control industrial infrastructure: power grids, water treatment, oil pipelines.
- DCS (Distributed Control Systems) — used in manufacturing and process industries for continuous production control.
- PLCs (Programmable Logic Controllers) — embedded industrial computers controlling specific machinery.
- ICS (Industrial Control Systems) — collective term for all industrial automation systems.
OT convergence with IT (OT/IT convergence) is one of the defining infrastructure challenges of 2026. As factories, utilities, and logistics operations connect OT systems to corporate IT networks and the internet (via Industry 4.0 / Industrial IoT), security vulnerabilities in OT — historically isolated from cyber threats — become enterprise-level risks. The Purdue Model (ISA-95 standard) defines the architecture for OT/IT integration across enterprise, control, and field levels.
Compliance Standards IT Teams Must Know
Beyond GDPR and CCPA, these compliance frameworks directly fall within IT governance:
- SOC 2 (System and Organization Controls 2): American Institute of CPAs (AICPA) audit framework — evaluates controls for security, availability, processing integrity, confidentiality, and privacy (the five Trust Services Criteria). SOC 2 Type I = controls design at a point in time; SOC 2 Type II = controls operating effectiveness over a period (typically 6–12 months). Increasingly required by enterprise B2B customers as a vendor security prerequisite. Most SaaS companies pursue SOC 2 Type II between Series A and Series B.
- PCI-DSS (Payment Card Industry Data Security Standard): Developed by the PCI Security Standards Council (founded by Visa, Mastercard, American Express, Discover, JCB). Version 4.0 (2022) — 12 requirements covering network security, cardholder data protection, vulnerability management, access control, monitoring. Any company that processes, stores, or transmits credit card data must comply. Non-compliance penalties are contractual (fines from card brands) not statutory.
- HIPAA Security Rule: U.S. Department of HHS — mandates Administrative, Physical, and Technical safeguards for Electronic Protected Health Information (ePHI). Business Associate Agreements (BAAs) are required for any vendor handling ePHI. Fines scale from $127 to $1.9M per violation category per year.
- FedRAMP (Federal Risk and Authorization Management Program): U.S. government cloud security authorization framework — required for cloud service providers serving U.S. federal agencies. Three impact levels: Low, Moderate, High. The authorization process is intensive (12–24 months) but opens access to the federal market.
Core ITSM Concepts That Define IT Operations
ITIL 4’s service management framework centers on several key concepts that differentiate IT operations from general technology management:
- CMDB (Configuration Management Database): A centralized repository of IT asset records (configuration items/CIs) and their relationships. The CMDB is the “map” of an IT environment — tracking servers, software, networks, and how they interconnect. ServiceNow’s CMDB is the most widely deployed commercial implementation. A well-maintained CMDB accelerates incident resolution (knowing what’s connected to what) and enables impact analysis for change management.
- Incident Management: The ITIL process for restoring normal service operation as quickly as possible after an unplanned disruption. Incidents are categorized by severity (P1/P2/P3) with defined SLA response and resolution times. The incident lifecycle: Detection → Logging → Classification → Investigation → Resolution → Closure.
- Problem Management: The process of identifying and addressing the root cause of recurring incidents. A “problem” is the underlying cause of one or more incidents. Problem management uses Root Cause Analysis (RCA) techniques (5 Whys, Fishbone/Ishikawa diagrams, fault tree analysis) and produces Known Error records to document workarounds.
- Change Management (Change Enablement in ITIL 4): The process of controlling changes to IT systems to minimize risk and disruption. Change types: Standard changes (pre-approved, low risk), Normal changes (require CAB/Change Advisory Board review), Emergency changes (expedited for critical fixes). Change management is directly audited in SOX Section 404 IT General Controls.
Q: What is the difference between ICT, IT, and OT — and why does it matter for startups?
IT (Information Technology) manages digital information within an organization — servers, software, networks, and data systems. ICT (Information and Communications Technology) is the broader government/policy term that adds telecommunications to IT. OT (Operational Technology) controls physical processes — manufacturing equipment, SCADA systems, industrial automation. For most software startups, IT is the relevant domain. OT becomes relevant if your product integrates with industrial machinery, IoT devices, or critical infrastructure. ICT matters when interfacing with government procurement, international standards bodies, or telecommunications partnerships. As OT/IT convergence accelerates in Industry 4.0, security teams increasingly need expertise spanning all three.
Q: What are the minimum IT controls a startup should implement before Series A?
Before Series A, the minimum viable IT control set includes: (1) Identity and Access Management — SSO (Okta, Google Workspace) with MFA enforced for all users; least-privilege access principle. (2) Endpoint Management — MDM (mobile device management) via Jamf (macOS/iOS) or Microsoft Intune for all company devices; full-disk encryption enforced. (3) Data Backup and Recovery — automated, tested backups with defined RTO (Recovery Time Objective) and RPO (Recovery Point Objective); offsite/cloud backup copies. (4) Vulnerability Management — automated dependency scanning (Snyk, Dependabot) in CI/CD; annual penetration test. (5) Incident Response Plan — a documented, practiced runbook for security incidents. Most Series A investors and enterprise sales prospects will ask about SOC 2 Type II readiness; starting these controls early makes the audit significantly easier.
Additional IT Vendors, Governance Frameworks, and Financial Concepts
Data Platforms: Snowflake and Databricks
The modern data stack has created a distinct category of platforms that sit at the boundary of IT infrastructure and technology innovation:
- Snowflake — Cloud data warehouse (multi-cloud: AWS, Azure, GCP). Snowflake’s separation of storage and compute allows organizations to scale query performance independently of storage costs. The Snowflake Data Cloud enables secure data sharing between organizations without copying data. Market cap peaked at ~$120B (2021 IPO); as of 2024 revenue ~$3.6B with ~9,000 customers including Capital One, DoorDash, and Airbnb. Used by IT/data engineering teams as the primary analytical data warehouse.
- Databricks — Unified analytics platform built on Apache Spark — combines data engineering (ETL/ELT pipelines), data science (ML experiments), and data warehousing (Delta Lake). Founded by the original Apache Spark creators at UC Berkeley. Databricks’ Lakehouse architecture (Delta Lake + Unity Catalog) bridges the gap between data lakes and data warehouses. Revenue ~$1.6B ARR (2024); customer list includes Shell, Comcast, and Regeneron.
Cybersecurity Vendors: CrowdStrike and Palo Alto Networks
Enterprise IT security is dominated by a small number of platform vendors replacing point solutions:
- CrowdStrike — Endpoint Detection and Response (EDR) and eXtended Detection and Response (XDR) platform. CrowdStrike Falcon is the market-leading cloud-native endpoint security agent, monitoring behavioral signals rather than signature-based detection. CrowdStrike’s Threat Intelligence team (Adversary Intelligence) tracks nation-state actors and publishes widely cited threat reports. Revenue $3.7B FY2024; ~29,000 customers. The July 2024 Falcon sensor update outage (affecting 8.5M Windows systems) demonstrated the systemic risk of endpoint security in critical IT infrastructure.
- Palo Alto Networks — Network security and cloud security platform vendor. Palo Alto’s next-generation firewalls (NGFW) introduced application-layer inspection (App-ID) replacing traditional port-based firewall rules. Prisma Cloud is a CNAPP (Cloud Native Application Protection Platform) for cloud workload security. Revenue $8B FY2024; serves 80%+ of Fortune 100 companies. Palo Alto’s “platformization” strategy (consolidating point tools) drives enterprise IT vendor consolidation.
Enterprise Architecture: TOGAF
TOGAF (The Open Group Architecture Framework) is the world’s most widely adopted enterprise architecture (EA) framework — used by 80% of Global 50 companies (The Open Group, 2023). TOGAF provides a methodology (Architecture Development Method / ADM) for designing, planning, implementing, and governing enterprise information architecture. TOGAF categorizes architecture into four domains: Business Architecture, Data Architecture, Application Architecture, and Technology Architecture (BDAT). Certification levels: TOGAF Foundation (Level 1) and TOGAF Practitioner (Level 2). EA architects using TOGAF create architecture roadmaps that align IT investments with business strategy — directly relevant to the technology vs IT strategic planning discussion.
Business Continuity: RTO, RPO, and IT Resilience
Two metrics define how IT organizations design disaster recovery systems:
- RTO (Recovery Time Objective) — The maximum acceptable time to restore a system after a disruption. If RTO = 4 hours, the business must resume operations within 4 hours of an outage. Higher criticality systems (payment processing, customer-facing APIs) require RTOs measured in minutes; back-office systems may tolerate RTOs of hours or days.
- RPO (Recovery Point Objective) — The maximum acceptable data loss measured in time. If RPO = 1 hour, backups must capture data at least every hour. RPO drives backup frequency and replication strategy decisions (synchronous vs. asynchronous database replication).
RTO and RPO together define the Business Continuity Plan (BCP) and directly inform IT infrastructure investment — shorter RTOs and RPOs require more expensive high-availability architectures (active-active vs. active-passive failover, geographically distributed data centers).
IT Financial Concepts: TCO, Unit Economics, and FinOps
- TCO (Total Cost of Ownership) — Complete cost of an IT system over its lifetime, including acquisition, implementation, training, maintenance, and eventual decommissioning. TCO analysis is critical when comparing on-premises vs. cloud infrastructure — cloud appears cheaper in year 1 but may have higher TCO at scale due to egress costs, managed service premiums, and storage costs. Gartner’s TCO methodology is the standard framework for infrastructure comparison.
- Unit Economics for SaaS Infrastructure — Cost per API call, cost per active user, infrastructure cost as a percentage of gross margin. Venture-backed SaaS companies typically target infrastructure costs below 10-15% of revenue (gross margin consideration). “Infrastructure cost per customer” is a key metric Board presentations track as companies scale from Series A to Series C.
- FinOps (Cloud Financial Management) — The practice of managing cloud costs through organizational collaboration between engineering, finance, and business teams. The FinOps Foundation (finops.org) defines three maturity phases: Crawl (basic visibility), Walk (cost optimization), Run (continuous optimization). Tools: AWS Cost Explorer + Savings Plans, Azure Cost Management, Google Cloud Recommender, Apptio Cloudability, CloudHealth by VMware. Leading cloud-native companies establish dedicated FinOps teams once monthly cloud spend exceeds $500k.
Additional FAQ: Startup IT Decision Guide
When should a startup hire a CTO vs a CIO?
Pre-Seed/Seed: Hire a CTO (or technical co-founder) first — product technology defines your value proposition. IT is handled by whoever is most technical. Series A: CTO focus shifts to platform architecture and engineering leadership; a Head of IT or DevOps lead manages internal systems. Series B+: If you process sensitive data (healthcare, fintech, enterprise SaaS), hire a dedicated CISO and Head of IT/CIO to drive SOC 2 Type II, manage MDM, and establish IT governance. The rule of thumb: hire CTO first for product moat, CIO when operational complexity and compliance requirements justify it (typically at 50+ employees or when enterprise customers demand it).
How should a startup budget for technology (R&D) vs IT (operations and security)?
Industry benchmarks by stage: Pre-Seed/Seed: ~80% engineering/R&D, ~20% IT/infrastructure (cloud hosting, security basics). Series A: ~70% R&D, ~30% IT (cloud infrastructure scales with users; SOC 2 prep begins). Series B: ~60% R&D, ~40% IT (dedicated IT/security team, ERP evaluation, enterprise identity management). Pre-IPO: ~50/50 as compliance, audit, and IT governance costs grow significantly (SOX ITGCs, CISO hire, global infrastructure). IT spend as a % of revenue typically ranges from 3-6% for mature SaaS companies (Gartner IT Spending Benchmarks, 2024).
For practical application of these technology concepts in your business, see our Proven SEO Strategies to Grow Any Business guide. For how technology investments translate to brand building and customer loyalty, see our Corporate Gifting for Brand Recognition guide.
Recommended Resources
Related reading: How To Use Keyboard Shortcuts For Productivity (Bookmark Sharer).
Explore Ux Portfolio Tips For Beginners for additional insights.






